Enterprise Governance with Role-Based Access Control
RBAC is the governance backbone retail media networks need to cut security risk, speed onboarding and reclaim control of first‑party data.

Enterprise Governance with Role-Based Access Control
Managing access in retail media networks is a growing challenge, especially in Australia’s booming A$3 billion sector. Role-Based Access Control (RBAC) is emerging as a solution, streamlining permissions, improving compliance, and reducing security risks.
Here’s what you need to know:
- What is RBAC? Instead of assigning permissions to individuals, RBAC ties permissions to roles (e.g., "Campaign Manager" or "Finance Manager"). This makes access management more efficient and scalable.
- Why it matters: Without clear access controls, organisations face delays, compliance risks (e.g., GDPR fines up to 4% of global revenue), and security vulnerabilities.
- Key benefits: RBAC simplifies onboarding, reduces administrative workload, and ensures users only access what they need. It also creates a clear audit trail for regulatory compliance.
- Challenges: Overuse of roles can lead to "role proliferation", complicating management. In some cases, a hybrid model combining RBAC with attribute-based controls (ABAC) may be more effective.
RBAC is helping Australian retailers manage large-scale digital signage networks, ensuring secure and efficient access to sensitive shopper data and campaign insights. Platforms like Adflux CMS are leading the way, reducing provisioning times and improving governance for businesses navigating this fast-growing industry.
Role-Based Access Control (RBAC) Explained: How it works and when to use it
sbb-itb-c231c83
1. Role-Based Access Control (RBAC)
RBAC assigns permissions based on job roles rather than individual users. For example, instead of granting access to each person, a role like "Campaign Manager" is created with specific permissions and then assigned to relevant individuals. This approach makes managing access more efficient and scalable, especially in retail media networks where multiple stakeholders need controlled access.
In retail media networks, different teams have distinct responsibilities: Relationship Managers oversee consignments, Vendors handle inventory and pricing, and Finance teams manage reconciled data. Each group requires tailored access. Platforms like Adflux CMS leverage RBAC to centrally manage permissions across thousands of digital screens nationwide, ensuring consistent messaging and safeguarding sensitive campaign data from unauthorised access.
Scalability
RBAC becomes increasingly valuable as organisations grow. Instead of setting permissions for every new employee, predefined roles like "Vendor" or "Finance Manager" allow for quick onboarding. Hierarchical RBAC takes this further by enabling higher-level roles, such as "National Admin", to inherit permissions from roles like "Store Manager", reducing duplicate efforts.
In Australia, managing large-scale deployments of digital screen networks has shown the practical benefits of this scalability. Automated RBAC workflows can significantly cut down on time, reducing data access provisioning from weeks to minutes and trimming audit preparation efforts by up to 25%. However, as systems expand, organisations must guard against "role proliferation", where too many roles can complicate management.
Administrative Efficiency
Traditional access models often require manual updates to permissions whenever an employee changes roles or leaves, sometimes leading to "zombie" accounts - inactive accounts that still have access. RBAC simplifies this by applying updates at the role level, ensuring changes automatically reflect across all users assigned to that role.
"RBAC isn't about controlling people. It's about controlling drift." – LoginRadius
Compliance Capability
RBAC also supports compliance by creating an auditable record of access, which is critical for regulatory audits. It enforces the principle of Separation of Duties, ensuring, for example, that the person entering an invoice for ad space cannot also approve its payment.
In early 2026, a major Australian retail media network began the IAB Australia Retail Media Certification process. Spearheaded by General Manager Tiffany Chen, the initiative focuses on aligning measurement practices with industry standards, enhancing accountability and trust in performance reporting. By maintaining detailed access logs for sensitive campaign and financial data, RBAC plays a key role in this certification process, reinforcing strong governance.
Security Risk Reduction
Beyond compliance, RBAC helps reduce security risks by enforcing the Principle of Least Privilege. This principle ensures users only have the access necessary for their specific tasks, limiting the damage a compromised account could cause.
"RBAC ensures that every user has the minimum level of access required to perform their job functions." – Birla Pivot Tech
Research indicates that the gap between what access users need and what they actually have can predict the severity of data breaches. Organisations that use automated tools to fix access misconfigurations have reduced remediation times by 90%. Regular access reviews, such as quarterly audits, further help identify and remove unnecessary privileges, preventing "privilege creep" and strengthening overall security.
2. Traditional Access Control Models
Before the efficiency of RBAC, organisations relied on older models like DAC, MAC, and ACLs to manage access. Discretionary Access Control (DAC) lets data owners decide who can access their assets. While this works well for smaller teams, it poses security risks in larger organisations due to its flexible yet inconsistent permission assignments. On the other hand, Mandatory Access Control (MAC) enforces strict policies through a central administrator, basing access on the sensitivity of resources and the user's security clearance. This model is often used in high-security settings, such as government or military operations.
Access Control Lists (ACLs) provide fine-grained control at the object level, like specific files or databases. However, managing ACLs becomes overwhelming as organisations scale. In retail media networks with thousands of employees and intricate data systems, these traditional models often rely on ad hoc decisions rather than pre-defined rules. This can lead to over-permissioned accounts and the presence of ghost accounts - active credentials belonging to former employees - which significantly increase security risks.
Scalability
Manual access management can work for small organisations but quickly becomes impractical as the workforce grows beyond 100–200 employees. Traditional models demand administrators assign permissions individually to each user or object. As teams expand or roles shift, this process becomes error-prone and inefficient. Mark Stone, Senior Technical Writer at Concentric AI, explains:
"Managing access individually for every employee is highly inefficient and prone to error".
Administrative Efficiency
Companies still relying on spreadsheets or outdated systems face both productivity challenges and heightened security risks. Unlike RBAC, which simplifies access management by grouping permissions into predefined roles (e.g., "Store Manager" or "Regional Supervisor"), these older models require far more manual effort. This lack of automation can extend onboarding times from hours to days.
Compliance Capability
Traditional access models also fall short when it comes to meeting regulatory requirements like GDPR, HIPAA, and SOX. Without a structured framework, enforcing Separation of Duties - such as ensuring one person doesn't both create and approve invoices - becomes difficult. Additionally, the lack of visibility across multiple systems complicates the task of maintaining a unified view of access permissions, increasing compliance challenges and security vulnerabilities.
Security Risk Reduction
Data breaches, which can cost businesses over A$4 million on average, are often linked to compromised credentials. Traditional models tend to create over-permissioned accounts, where users have more access than necessary, and privilege creep, where users retain outdated permissions. By September 2021, data breaches had risen by 17% compared to the previous year, highlighting the dangers of inconsistent, manual access management. This underscores why a shift to RBAC is essential for retail media networks. RBAC's ability to streamline permissions not only reduces vulnerabilities but also ensures consistent security practices across the organisation.
Advantages and Disadvantages
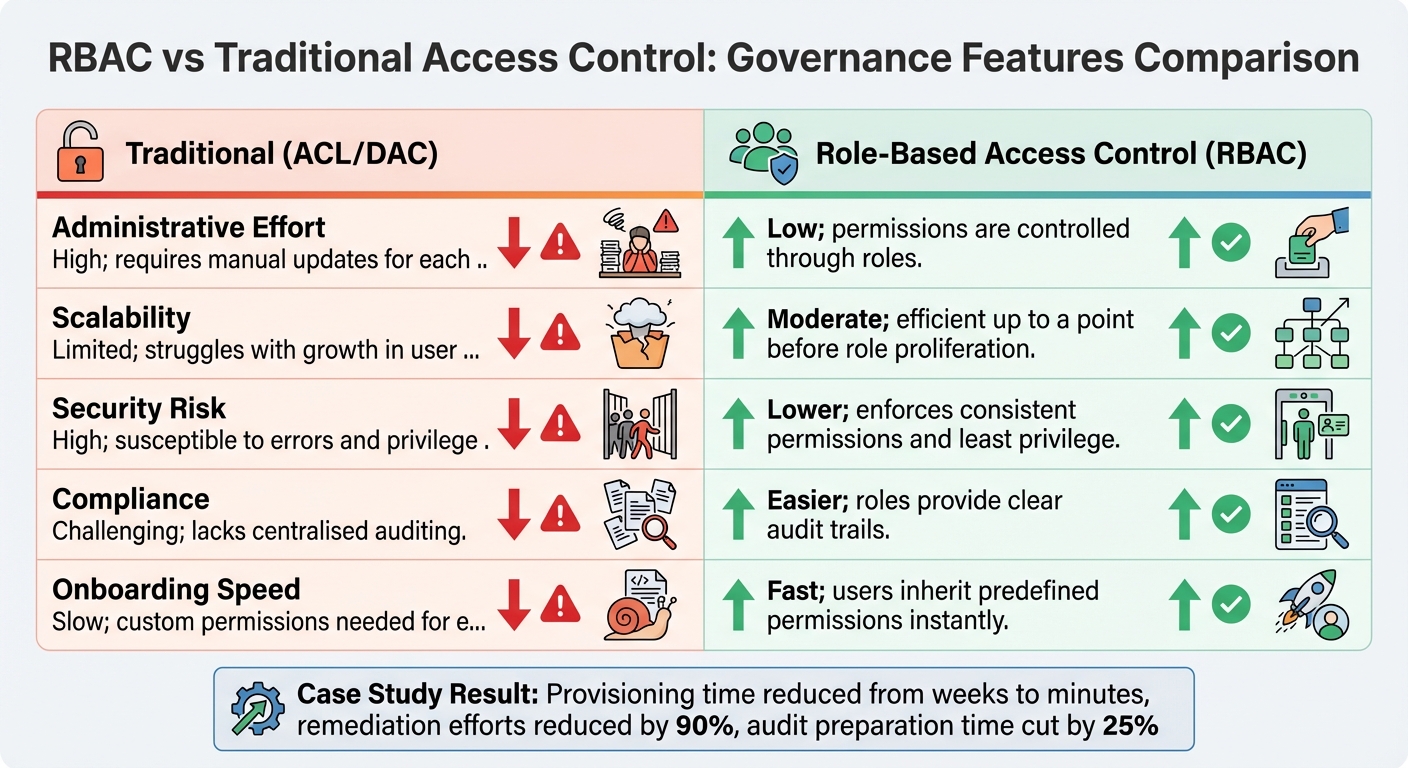
RBAC vs Traditional Access Control: Key Governance Features Comparison
RBAC (Role-Based Access Control) continues to stand out for its practicality in managing access, particularly in large organisations. By assigning permissions to roles instead of individuals, RBAC simplifies access management compared to traditional models like DAC (Discretionary Access Control) and ACLs (Access Control Lists), which rely on individual permission assignments. This distinction becomes especially apparent when considering factors like scalability, compliance, administrative efficiency, and security risk.
Here's a side-by-side comparison of key governance features:
| Feature | Traditional (ACL/DAC) | Role-Based Access Control (RBAC) |
|---|---|---|
| Administrative Effort | High; requires manual updates for each user | Low; permissions are controlled through roles |
| Scalability | Limited; struggles with growth in user numbers | Moderate; efficient up to a point before role proliferation |
| Security Risk | High; susceptible to errors and privilege creep | Lower; enforces consistent permissions and least privilege |
| Compliance | Challenging; lacks centralised auditing | Easier; roles provide clear audit trails |
| Onboarding Speed | Slow; custom permissions needed for each user | Fast; users inherit predefined permissions instantly |
These distinctions aren't just theoretical - they're backed by real-world examples. For instance, a 2026 case study highlighted a Fortune 500 healthcare organisation that streamlined its RBAC system across platforms like Snowflake and Databricks. The results? Provisioning time dropped from weeks to minutes, remediation efforts were reduced by 90%, and audit preparation time was cut by 25%.
However, RBAC isn't without its challenges. In environments with highly dynamic or complex access requirements, like retail media networks, organisations often face what's known as "role explosion." This occurs when the number of roles grows disproportionately to the number of users. A retail grocery chain with 340 stores and 2,040 users, for example, initially managed 2,788 unique policies due to store-specific roles and high user turnover. By transitioning to an attribute-based model (ABAC), they reduced this number to just three policies.
As LoginRadius explains:
"Role explosion is not a failure of the people managing roles. It is an inherent limitation of the RBAC model when applied to environments with complex, dynamic access requirements".
Despite these challenges, RBAC remains a powerful tool for improving compliance, reducing administrative burden, and enforcing security principles like least privilege. For organisations with evolving needs, a hybrid approach that combines RBAC's strengths with the flexibility of ABAC can provide a balanced solution. Understanding these trade-offs is crucial for building an effective and scalable access governance strategy.
Conclusion
Australia's retail media networks, now part of a booming A$3 billion market, can greatly benefit from Role-Based Access Control (RBAC). This governance framework not only reduces the administrative workload but also speeds up onboarding, enforces strict security protocols like least privilege access, and ensures compliance with Australia's regulatory requirements.
With insider threats accounting for 60% of data breaches and nearly half of tech employees admitting to data breaches when leaving or after dismissal, relying on manual permission management is a dangerous gamble. Centralising access control and automating how permissions are updated ensures that role changes or departures don't leave behind security gaps. These figures highlight why integrated solutions are critical in this fast-evolving retail media environment.
Take Adflux CMS as an example. For retailers managing hundreds of digital screens, RBAC simplifies operations with multi-user support and detailed role assignments. A "Store Manager" can handle local content updates, while a "Marketing Manager" oversees campaigns - all without compromising sensitive customer data or administrative control. This setup prevents unauthorised access while maintaining operational efficiency.
Regular audits are another key advantage of RBAC. They ensure permissions adapt to organisational shifts, avoiding the common issue of "permission creep" seen in older models. For businesses juggling the diverse access needs of external brands, internal teams, and store-level staff, the takeaway is clear: roles should align with actual job responsibilities, permissions should be limited to what's necessary, and governance must be actively maintained.
As Australia's retail media sector continues to grow, governance frameworks like RBAC will become even more essential. With 70% of advertisers and agencies planning to increase their investments between 2024 and 2025, adopting RBAC isn't just about operational efficiency - it's about safeguarding first-party customer data, ensuring brand safety, and fostering the trust that fuels successful partnerships in this thriving industry.
FAQs
How do we choose the right RBAC roles for our retail media teams?
To determine the right RBAC roles, start by aligning them with specific team functions and their access requirements. Identify the main responsibilities for each group - like administrators, sales teams, or content managers - and assign permissions that match their tasks. For instance, administrators might need full access, while sales staff could require restricted permissions to handle campaigns. Customising roles to limit unnecessary access not only strengthens security but also ensures smoother governance and efficiency in managing retail media operations.
How does RBAC stop ex-staff and contractors from keeping access?
RBAC helps prevent former employees and contractors from retaining access by quickly updating or revoking their roles and permissions within the system. This approach safeguards sensitive resources and supports enterprise governance.
When should ABAC be added to RBAC to avoid role explosion?
When role explosion happens in RBAC (Role-Based Access Control), adding ABAC (Attribute-Based Access Control) can be a smart move. By integrating ABAC, you can cut down on the need to create overly specific roles, which often complicate access management. This approach helps reduce risks, eliminate blind spots, and simplify the process, making access controls easier to manage and more scalable in the long run.
Adflux Editorial
Retail media, programmatic DOOH, and digital signage insights for Australian retailers.
Ready to build your retail media network?
Talk to the Adflux team about how the platform can work for your screens.